Assess cloud security maturity and risk
Cybersecurity
Automated infrastructure demands automated security. iShift delivers strategic cybersecurity leadership and hands-on execution, embedding protection into your cloud so security scales with your business.

CISO on Demand by iShift
Security leadership isn’t about a title. It is about results. iShift’s Fractional CISO offering delivers measurable risk reduction by connecting cybersecurity strategy directly to execution. We don’t stop at guidance and policies. We turn decisions into action by pairing senior security leadership with the technical teams and cloud expertise needed to implement, operate, and evolve your security program.
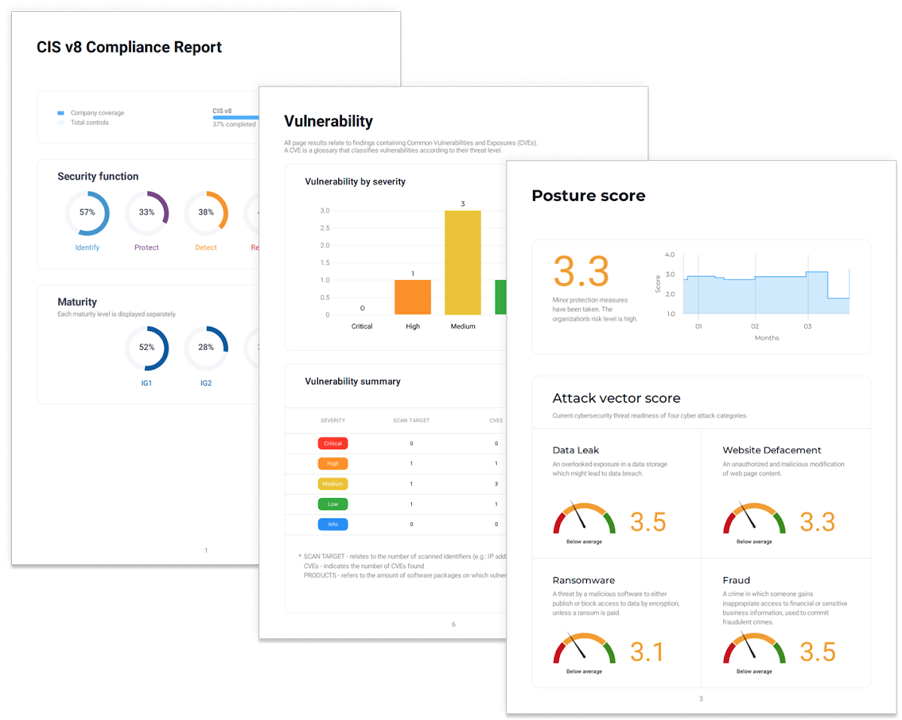
iCompli, iShift's AI-Powered Risk Management Platform
Cloud environments evolve in real time and security has to keep up. iCompli replaces slow, manual security processes with controls that operate continuously inside your cloud. The result is faster delivery, reduced risk, and compliance that keeps pace with change. Eliminate blind spots and reducing friction so your teams can move faster while staying audit-ready and secure by design with the iCompli GRC platform.

Identity and Access Management Solutions
Security breaks down when access isn’t aligned to intent. iShift’s Identity and Access Management solutions ensure the right users have the right access only when they need it. By enforcing least privilege, automating access lifecycle management, and continuously validating identity, we reduce attack surface, improve audit readiness, and enable teams to move faster without compromising control.

Automated Risk Assessments
Don’t wait for a security incident to reveal your vulnerabilities. iShift’s Risk Assessments proactively identify and prioritize cybersecurity risks across your organization and provide you the insights needed to protect your business, satisfy compliance requirements, and build stakeholder confidence. Our expert assessments combine comprehensive technical analysis with strategic guidance and deliver clear recommendations that align security investments with your business priorities.

Penetration Testing
Most penetration tests deliver overwhelming lists of technical vulnerabilities with no context on business impact or remediation priority. iShift’s approach is different: we simulate real attack scenarios to identify the exploitable weaknesses that actually threaten your business and then provide strategic guidance on what to fix first based on risk, effort, and business impact. Our experienced security professionals combine technical depth with business acumen and translate technical findings into executive-ready reports that demonstrate security posture to boards, customers, and regulators. Beyond identifying vulnerabilities, we validate your security investments, reveal gaps in defense-in-depth strategies, and provide actionable roadmaps that measurably reduce risk.

Backup & DR
Data loss isn’t a question of if but of when and your ability to recover determines whether it is a minor inconvenience or a business-ending catastrophe. iShift’s Backup & Disaster Recovery services combine automated cloud-based backups with comprehensive recovery planning to protect your organization from ransomware, system failures, and unexpected disasters. We design solutions tailored to your Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO), ensuring critical systems can be restored within minutes or hours, not days. From Microsoft 365 data protection and cloud workload backup to complete disaster recovery orchestration, our services leverage modern cloud platforms to deliver resilience without the overhead of maintaining secondary data centers.
When security can’t match cloud velocity, organizations face:
Security teams are forced into a reactive posture chasing issues after deployments instead of preventing them by design.
Hidden Risk
Shadow IT, misconfigurations, and over-privileged access proliferate faster than teams can detect them.
Compliance Drift
Policies applied at a point in time quickly fall out of sync with reality.
Alert Fatigue
Security teams drown in findings but lack context or prioritization.
Slower Innovation
Developers wait on approvals while competitor products ship faster.
Our Approach
Security Transformation in Three Phases
Comprehensive security posture assessment, threat modeling, and architecture design aligned with your business risk profile and compliance requirements.
Implement security automation, integrate controls into CI/CD pipelines, and establish policy-as-code foundations for scalable security operations.
Continuous security monitoring, threat intelligence integration, and ongoing optimization of security controls based on emerging threats and business needs.

Autonomous Security at Cloud Speed
iShift’s Security-First Architecture embeds security directly into your cloud infrastructure, making secure-by-default the path of least resistance through automation, intelligent monitoring, and continuous compliance. Transform security from a compliance checkbox into your competitive advantage with autonomous, intelligent cloud architecture.
Zero Trust Architecture

Implement never-trust, always-verify security models that eliminate the concept of a trusted network perimeter.
->Identity-based access controls with continuous verification
->Micro-segmentation and least-privilege networking
->End-to-end encryption for data in transit and at rest
->Context-aware access policies based on device, location, and behavior
Infrastructure as Code Security
Security policies codified and version-controlled alongside your infrastructure, ensuring every deployment meets security standards automatically.
->Policy-as-code enforcement (OPA, Sentinel, Cloud Custodian)
->Automated security scanning in CI/CD pipelines
->Immutable infrastructure preventing configuration drift
->Git-based audit trails for all security changes
Intelligent Threat Detection
AI-powered security monitoring that identifies anomalies, predicts threats, and responds autonomously to reduce mean time to remediation.
->Behavioral analytics and anomaly detection
->Automated incident response playbooks
->Real-time threat intelligence integration
->Predictive risk scoring and prioritization
Continuous Compliance

Real-time compliance monitoring and automated remediation that maintains regulatory adherence without manual intervention.
->Automated compliance frameworks (SOC 2, HIPAA, PCI-DSS, GDPR)
->Continuous control monitoring and validation
->Auto-remediation of policy violations
->Evidence collection and audit-ready reporting
Supported Security Frameworks






Chosen by 150+ Companies
20+ years of Cloud Expertise
Let's work with your teams to:
Trusted by global companies
Get in Touch
Let’s start with a quick chat.
iShift’s cloud experience made our migration fast and seamless while keeping our data integrity and business continuity intact. Our collaboration is a true partnership.
kr